Introduction of MAC
Message authentication is a mechanism or service used to verify the integrity of a message. Message authentication guarantees that the sender of the message is authentic.
 |
| Figure: Block Diagram of MAC |
A MAC
algorithm, sometimes called a keyed hash function accepts as input a secret key
an arbitrary-length message to be authenticated, and outputs a MAC. MAC value
protects both a message’s data integrity as well as its authenticity, by
allowing verifies to detect any changes. The MAC is a small fixed-size block of
data that is generated based on a message M of variable length using secret key
K as follows. MAC is also called cryptographic checksum.
MAC = C (K,
M)
Application of MAC
#1 Message Authentication
 |
Figure: Message Authentication |
Sender A
want to send message to B via MAC, then the first condition is to share a secret
key K. Sender A calculates the MAC from message M by applying K. Append MAC to
the message M. A sends the original message M and the MAC to B. When B receives
message, B also uses K to calculate own MAC over message M. B now compares MAC1
and MAC2. If both are same, B assures that message is not altered during
transmission. If it is not matched, it means B can reject the message.
#2 Message Authentication and
Confidentiality; Authentication tied to plain text
 |
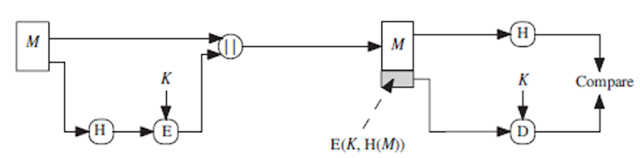
Figure: Message Authentication and Confidentiality |
Sender A
want to send message to B via MAC, then the first condition is to share a
secret key K1. Sender A calculates the MAC from message M by applying K1.
Append MAC to the message M. Encrypt message and appended MAC using key K2. A
sends the generate cipher text (Message + MAC) to B. When B receives cipher
text, decrypt using key K2. B also uses K1 to calculate own MAC over message M.
B now compares MAC1 and MAC2. If both are same, B assures that message is not
altered during transmission. If it is not matched, it means B can reject the
message.
#3 Message Authentication and
Confidentiality; Authentication tied to cipher text
 |
Figure: Message Authentication and Confidentiality |
Sender A
want to send message to B via MAC, then the first condition is to share a
secret key K1. Sender A encrypt the message and generate cipher text using key
K 2. Sender A calculates the MAC from cipher text by applying K1. Then append
MAC to cipher text. A send appended cipher text plus MAC to B. When B receives
message, B also uses K1 to calculate own MAC over message M. Decrypt ciphertext
using K2 and get original message. B now compares MAC1 and MAC2. If both are
same, B assures that message is not altered during transmission. If it is not
matched, it means B can reject the message.
Importance of MAC:
MAC
ensures that only receiver can identify the original message. Even if attacker
modifies the message M, but cannot modify MAC. In case of MAC is modified by
attacker, receiver’s calculations of MAC will differ from it. MAC cannot modify
easily because MAC is encrypted by secret key K, but key is only known by
sender and receiver only. MAC in one-way function. MAC provides data integrity
and authentication both. Also apply encryption and achieve confidentiality.
To learn more about Introduction of MAC & it's Applications, Click here
Watch more videos click here.